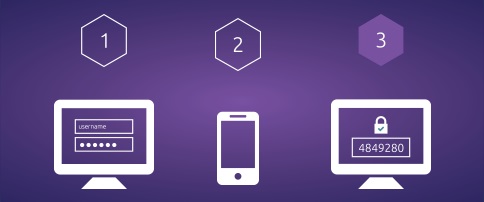
Simple two-factor authentication: integrates a time-based, one-time password solution into CA Single Sign-On.
CA Single Sign-On (formerly SiteMinder) provides a centralized security management foundation that enables the secure use of the web to deliver applications to customers, partners and employees.
Now, with IDF Connect’s SSO/Mobile Key, CA SSO can easily provide simple, secure, and strong two-factor authentication between your users and applications.
Use Google Authenticator or any other compatible OTP smartphone app.
One Strong Authentication Solution for Every CA SSO Application
Ease of Integration
The IDF Connect one-time password (OTP) solution introduces no new moving parts. Authentication is enforced entirely by CA SSO and administration is performed entirely within CA IdentityMinder.
Simplify
Registration and management of user tokens occurs entirely within either IdentityMinder or a provided standalone Java web application.
Try a free online DEMO of IDF Connect’s SSO/MobileKey demonstrating authentication best practices at IDFConnect.net
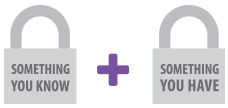
Two-factor authentication (2FA) provides unambiguous identification and authentication of users by means of combining ”something you know” (password) with “something you have” (mobile device) and enables the software to calculate the unique OTP for each user.
This solution will work with any mobile device app supporting an RFC-6238 two-factor OTP solution, such as Google Authenticator.
IDF Connect’s SSO/MobileKey solution for CA Single Sign-On (formerly SiteMinder):
- Secures access to networks and applications
- Protects users
- Addresses compliance requirements for the protection of regulated data
- Simplifies deployment and management
- Improves user experience
- Minimizes the cost and complexity of implementing traditional hardware tokens
Features
IDF Connect’s SSO/MobileKey solution:
- Introduces no new moving parts
- Authentication is enforced entirely within CA SSO using a single, configuration-less library — no new applications or running services.
- Management of user tokens happens entirely within IdentityMinder or a provided standalone java web application.
- Supports six or eight digit pins
- Supports SHA1 or SHA2 (256 and 512 bit) MAC (hash) algorithms
- Supports variable validation windows (the length of time that a pin is valid, with a default of 30 seconds)
- Able to issue multiple tokens to users
- For multiple applications with different security requirements, the solution allows you to configure as many “issuers” as required.
- Use in conjunction with CA SSO’s built-in RADIUS server to extend authentication to network and VPN devices
- Supports token expiration and re-issue (e.g. you can set tokens to expire every two years)
- Configurable next-token and token disable thresholds
- After a defined number of invalid login attempts, next-token mode is triggered, where the user is required to enter two consecutive tokens as a security measure against brute-force attacks.
- When tokens are eventually disabled multiple re-enablement methods available, such as time (e.g. after one hour) or after an alternative challenge (e.g. user security challenge questions, or a one-time password sent via SMS).